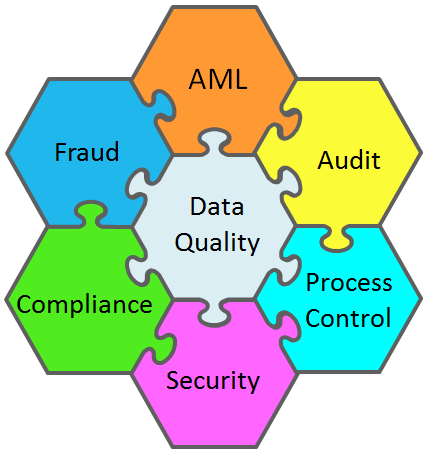
Industry Horizontal
- Data Quality Governance
- Compliance
- Internal Audit
- External Audit
- Operational Risk
- Financial Fraud
- Anti-Money Laundering
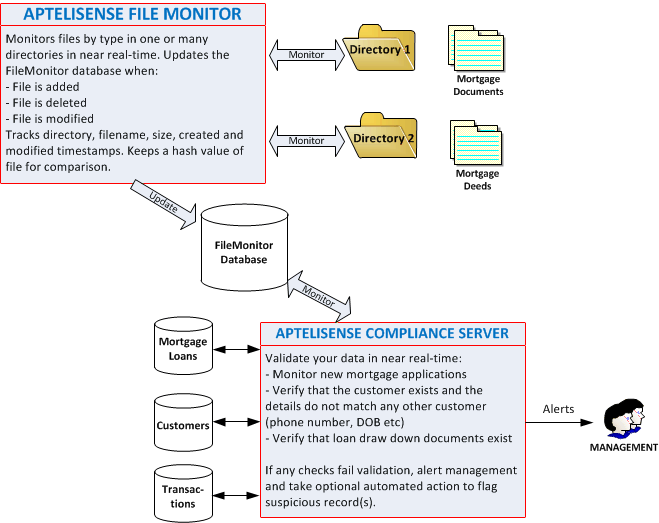
- Mortgage Fraud
- Business Process Improvement
- Intelligence
- Database Access Monitoring
Industry Vertical
Solution Vertical
Products
Tools
SolutionsIndustry HorizontalData Quality and GovernanceCompliance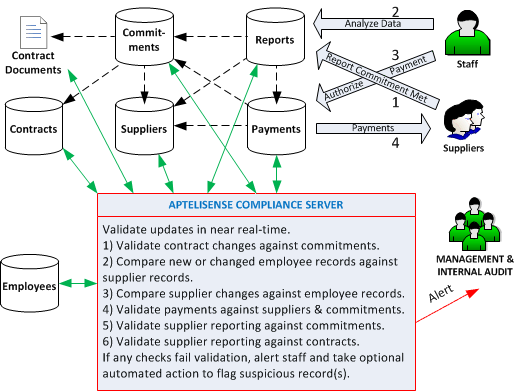
Internal Audit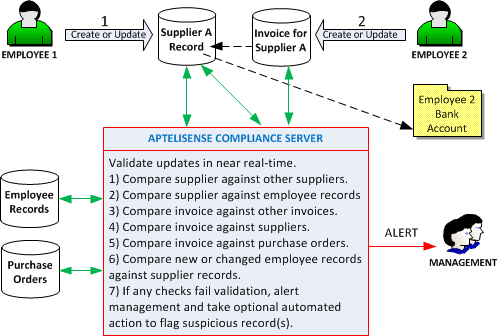
External AuditOperational RiskFinancial Fraud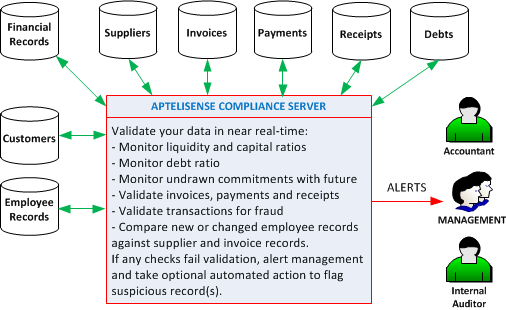
Anti-Money LaunderingMortgage FraudBusiness Process ImprovementIntelligenceDatabase Access MonitoringIndustry VerticalBanking and Finance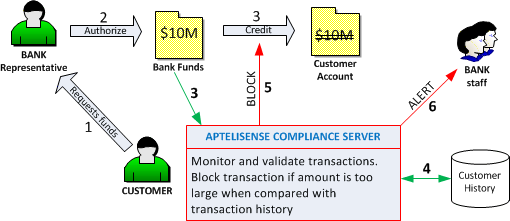
InsuranceGovernmentTelecommunicationsSolution VerticalEnable IBM i2 to access your enterprise data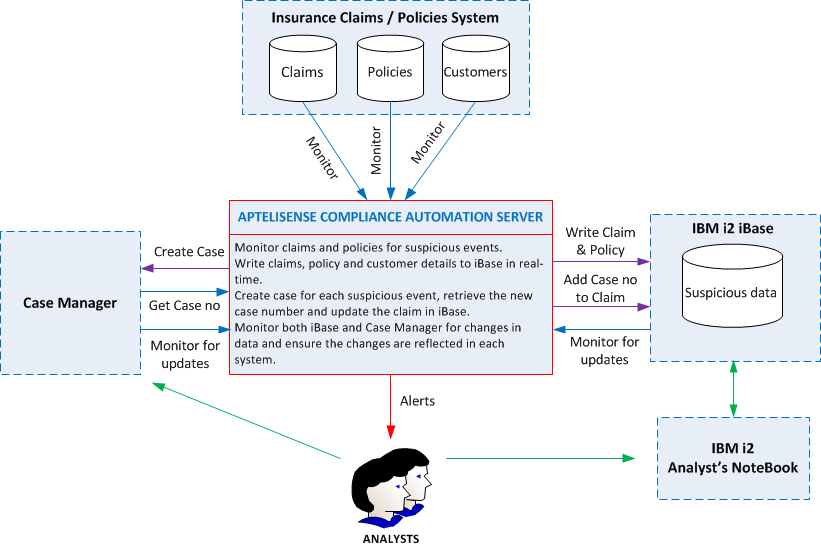
Cash Management In Banks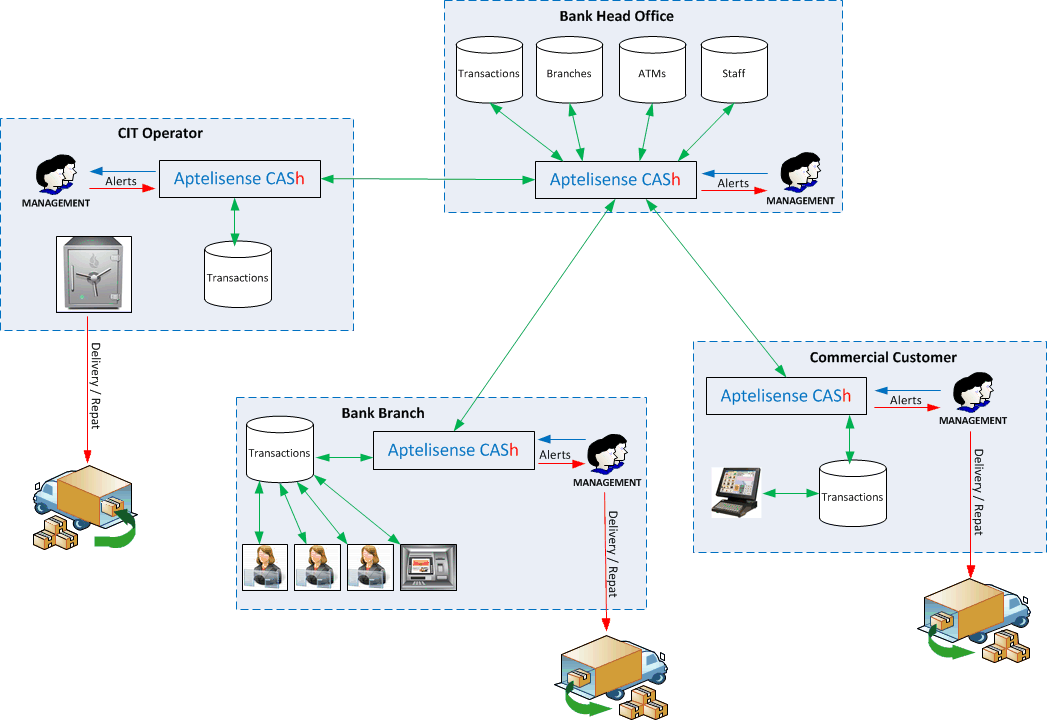
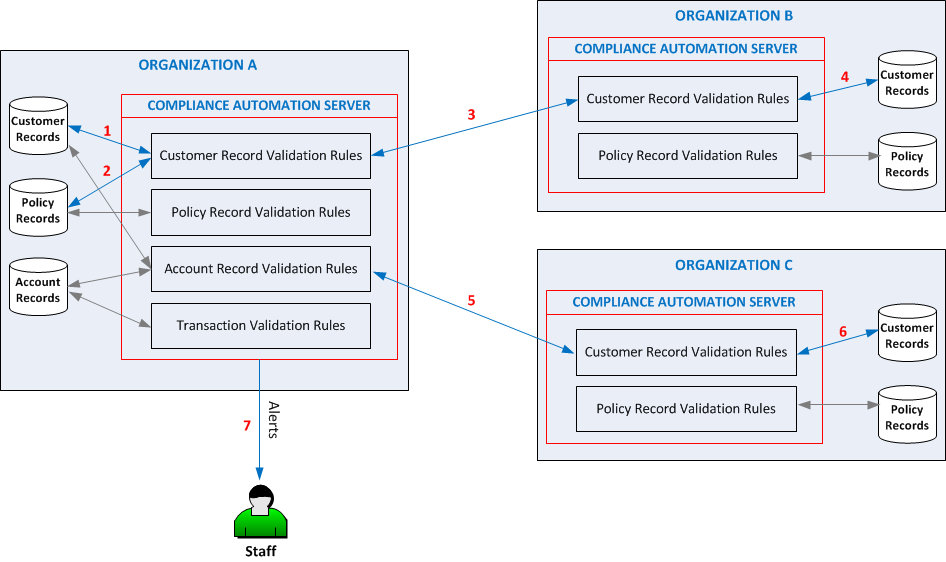
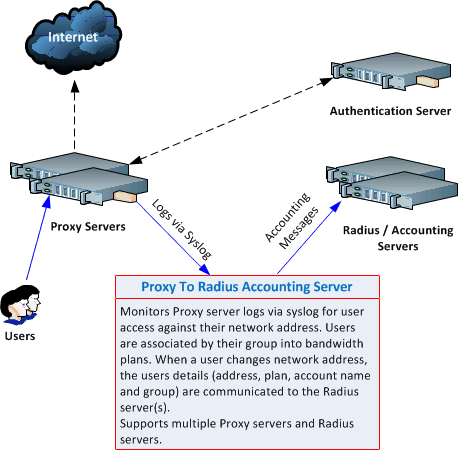
ProductsCompliance Automation ServerPro ClientAptelisense Membership FrameworkProxy to RadiusToolsIntelligent Matching EngineFile Monitor |
©2024 Aptelisense NZ Ltd. All Rights Reserved.




 The lack of control over data quality can have a compounded effect on your organization. The evidence of this will start to be visible
when reports from different systems or tools highlight inconsistencies. Along side this there will be random quality issues with application
behavior and business intelligence may not be as accurate as expected. Customers may start to see these issues when it becomes apparent
that their details are not the same across products and they may experience difficulties trying to change some of their personal details.
The lack of control over data quality can have a compounded effect on your organization. The evidence of this will start to be visible
when reports from different systems or tools highlight inconsistencies. Along side this there will be random quality issues with application
behavior and business intelligence may not be as accurate as expected. Customers may start to see these issues when it becomes apparent
that their details are not the same across products and they may experience difficulties trying to change some of their personal details.